Hi Jeff, welcome to the forums!
Ok, so to start with, your requirement is fairly typical and there are multiple easy ways to do what you want to do. To get there however I need to add a little background.
There are essentially three components to what you want to do.
- Hosting the application,
- Connecting the application to the Internet
- Finding the application on the Internet
Starting with the last part as that’s probably the easiest. Typically a domain name is used to cover naming for your organisation, rather than just one resource, like a website. So typically people would use www.domainname for their website, where www is the resource in question, then they might have mail.domainname, wiki.domainname etc etc.
Now it has become common practice to drop the “www” for websites, however physically the naming mechanism hasn’t changed. Although there are different ways of setting things up, the “norm” in this case would be to create an “A” record with your DNS provider for something like “myapp.domainname”, which points to the address of whatever you are going to expose to the Internet. Then instead of doing a “get” against “domainname”, do a GET against “myapp.domainname”.
So in terms of hosting and connectivity, I’m working on the basis that your app is hosted on an RPi, and that Flask is also running on the RPi. In this case I would look to expose the RPi to the Internet via a tunnel, then point “myapp.domainname” at the public end of the tunnel.
Sounds hard / complicated, but it’s really not so long as you have the right tools and are prepared to use them as intended 
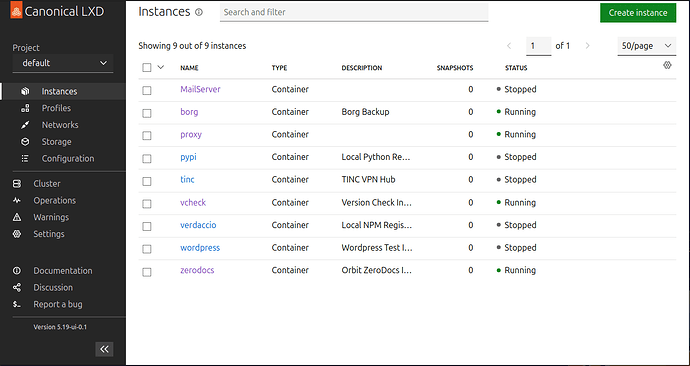
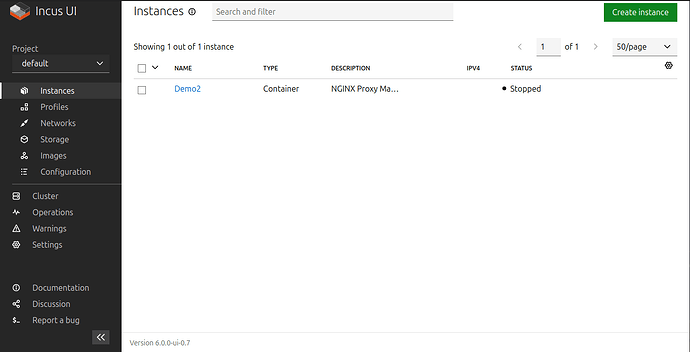
So, I am actually doing something very similar to you, albeit on maybe a larger scale. I’m running a bunch of things “here”, exposing them via tunnels and pointing names at them. If you’d like to try an example, take a look at;
https://zerodocs.madpenguin.uk
This is a Python/Javascript application that’s running inside a “container” on a Raspberry Pi4 and as it happens, managed by “systemd” as per your DO article 
So assuming you already have the Raspberry Pi / Flask set up and running, it’s the tunnel and domain name to play with.
Tunnels & Domains
For both of these I use CloudFlare. They run a “free tier” so the tunnel function isn’t something you need to pay for. In terms of tunnel management and domains, it’s relatively automated, but in order to do this, CloudFlare need to be able to manage the domain. So the first thing I’d recommend it to use CloudFlare as your registry, then just point the domain name at your WIX website for continuety.
Once you’ve done this, on the CloudFlare dashboard (once you have a free account) take a look at the “Zero Trust” menu option, then within this “Tunnels”, then “Create a tunnel”. Select the default connector and hit “next”. Give it a name then click “save”.
Now you need to set up the RPi end. Click on the button for your distribution (on the CloudFlare dash - I use debian) and then for your architecture, which will be arm64 for a RPi, then click on the two overlapping squares icon (which does a clipboard copy). Now go to a SSH or console session on your RPi and paste in what you just copied. That should install the tunnel and connect it up.
If you go back to the CloudFlare page and click “Next”, it will prompt you for a subdomain, so you will want whatever name (like “myapp”) you want to use. Then select your domain from the drop-down. Now you need to tell it what to do when it gets to your end of the tunnel, so select HTTP from the drop-down (I’m guessing you’ve not set up SSL?) and then “localhost:port” for the URL, where “port” is the port you have flask running on, so if it’s on port 80, then “localhost:80”.
Cloudflare should then automatically set up “myapp.domainname”, install an SSL certificate for you (on it’s end) and make “https://myapp.domainname” live in such a way that requests are serviced by your Flask application …
Again, once you start playing with it you realise CloudFlare are doing 99% of the work for you and all you really need to know is what you want to do and how to navigate their dashboards …